How Sharing a Password Can Destroy Your Document Security | Happierleads

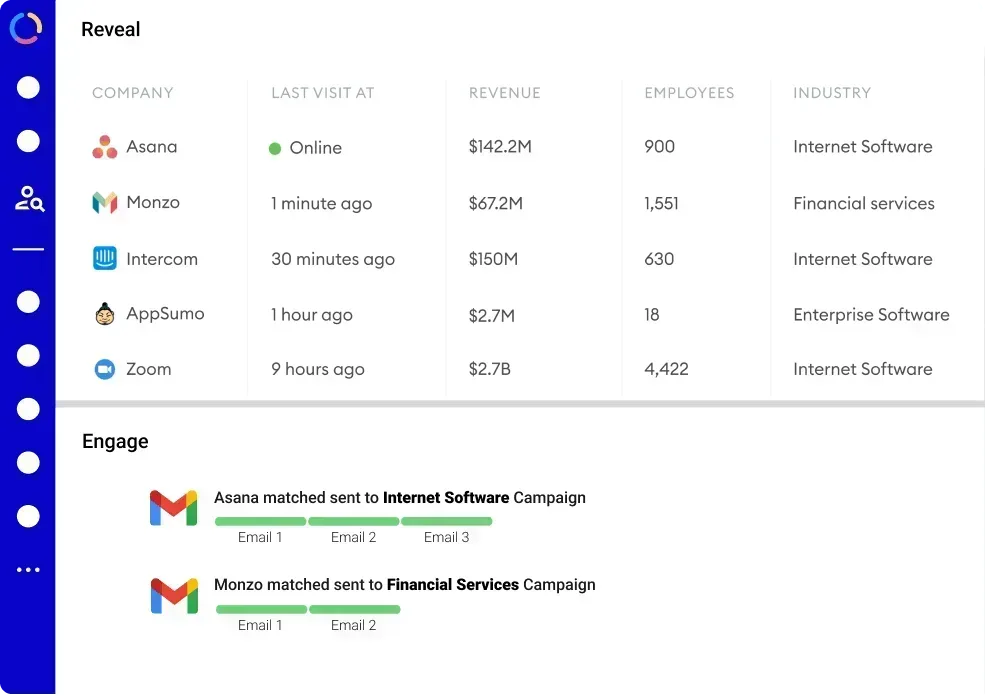
See the exact people visiting your website and Follow up with them.
Picture this: you've meticulously crafted a vital business proposal filled with confidential data and unique insights. To expedite feedback, you decide to share the document's password with a trusted colleague. It seems innocuous—after all, it's just a single password shared with someone reliable. However, this seemingly minor action can dismantle your entire document security framework.

The Hidden Dangers of Password Sharing
While sharing passwords might seem like a convenient shortcut, it actually opens a Pandora's box of security vulnerabilities. By handing over a password, you relinquish control over who can access your documents. Even if the recipient is trustworthy, there's no assurance that the password won't be forwarded, written down, or stored insecurely.
A 2023 report by the cybersecurity firm NordPass revealed that 50% of individuals admit to sharing passwords with colleagues or friends. This widespread practice significantly heightens the risk of unauthorized access. Once a password is shared, tracking its journey or preventing its misuse becomes nearly impossible.
Unintended Recipients and Data Exposure
Passwords are often shared via email, chat apps, or sticky notes—methods susceptible to interception or accidental exposure. If a password lands in the wrong hands, sensitive documents can be downloaded, altered, or deleted without your knowledge. This can lead to data breaches, loss of intellectual property, or compliance violations.
In sectors like finance, healthcare, or legal services, where regulatory requirements are stringent, such breaches can result in substantial fines and reputational damage. Even in less regulated industries, the fallout from leaked confidential information can be catastrophic, affecting customer trust and long-term business relationships.
Password sharing can foster a false sense of security. Users may believe that sharing access with colleagues is harmless, but this can lead to a culture of negligence regarding cybersecurity practices. Employees might feel less inclined to use strong, unique passwords if they think they can simply share them with others. This mindset perpetuates a cycle of poor security habits, making organizations more vulnerable to cyberattacks. As cybercriminals become increasingly sophisticated, relying on shared passwords is akin to leaving the front door wide open, inviting trouble right in.
Why Password Sharing Undermines Document Integrity
Document security isn't just about locking files away; it's about maintaining control over who can view and edit information. When passwords are shared, accountability vanishes. You can no longer be sure who made changes or when they occurred. This lack of accountability can lead to significant issues, especially in environments where sensitive information is handled, such as legal or financial sectors. The potential for unauthorized access increases, and the risk of data breaches escalates, putting both individuals and organizations at risk.
Lack of Audit Trails
Most document management systems provide audit logs that track user activity—who accessed a file, what changes were made, and when. But if multiple people use the same password, these logs become meaningless. You can't distinguish between users, making it impossible to identify the source of errors or malicious edits. This not only complicates the process of tracking down issues but also undermines trust among team members. In a professional setting, knowing that every action is accountable fosters a culture of responsibility and diligence, which is lost when passwords are shared indiscriminately.
Compromised Version Control
Shared passwords can lead to conflicting edits and version confusion. When several people access a document under the same credentials, coordinating updates becomes chaotic. This increases the risk of overwriting important information or circulating outdated versions, which can have serious consequences in collaborative environments. The inability to manage versions effectively can lead to wasted time as team members may find themselves working on different iterations of the same document, causing frustration and inefficiency. In industries where precision is critical, such as healthcare or engineering, the ramifications of such errors can be dire, potentially affecting decision-making processes and outcomes.
The implications of password sharing extend beyond immediate document management issues. It can create a culture of negligence regarding security practices. When team members see shared passwords as a norm, they may become lax in other areas of cybersecurity, such as recognizing phishing attempts or maintaining personal password hygiene. This collective disregard can lead to a broader vulnerability, making organizations easy targets for cybercriminals who exploit weak security protocols.
How Password Sharing Puts Your Entire Network at Risk
Passwords are often the first line of defense, but they rarely protect just one document. Many users reuse passwords across multiple files or even different platforms. Sharing a single password can therefore expose a wide range of sensitive data.
The Domino Effect of Credential Compromise
If a password used for document access is compromised, attackers might try the same credentials on other systems, a tactic known as credential stuffing. This can lead to unauthorized access to email accounts, cloud storage, or internal networks, magnifying the damage exponentially.
In 2022, IBM's Cost of a Data Breach Report highlighted that compromised credentials were involved in 20% of data breaches globally. This statistic underscores how critical it is to protect passwords and avoid sharing them.
Better Alternatives to Sharing Passwords
There are smarter ways to collaborate securely without handing over passwords. Modern tools and best practices can help maintain document security while enabling efficient teamwork.
Use Role-Based Access Controls
Instead of sharing passwords, assign specific access rights to individual users. Role-based access control (RBAC) restricts document permissions based on a user's role, ensuring they only see or edit what they're authorized to. This approach maintains accountability and limits exposure.
Leverage Secure Collaboration Platforms
Cloud services like Google Workspace, Microsoft 365, or specialized document management systems offer built-in sharing features that don't require password exchange. These platforms allow users to share links with controlled permissions, expiration dates, and activity tracking.
Implement Multi-Factor Authentication (MFA)
MFA adds an extra layer of security by requiring users to verify their identity through a second factor, such as a mobile app or hardware token. Even if a password is compromised, unauthorized access becomes much harder.
Utilize DRM and Encryption
Digital Rights Management (DRM) and encryption are powerful tools for protecting documents. DRM controls how documents are used and shared, while encryption secures the content by converting it into a code that only authorized users can decrypt. These methods ensure that even if a document is accessed, its contents remain protected from unauthorized viewing or editing.
Creating a Culture of Security Awareness
Technical solutions alone aren't enough. Organizations must foster a culture where employees understand the risks of password sharing and commit to secure practices.
Regular Training and Clear Policies
Training sessions that explain why password sharing is dangerous and how to use secure collaboration tools can significantly reduce risky behavior. Clear, enforceable policies should outline acceptable sharing methods and consequences for violations.
Encourage Reporting and Support
Employees should feel comfortable reporting lost or compromised credentials without fear of blame. Providing easy access to IT support for password resets or access requests helps prevent insecure workarounds.
Final Thoughts
Sharing a password might seem like a quick fix, but it can unravel your entire document security framework. The risks include unauthorized access, loss of accountability, version control issues, and broader network vulnerabilities. By adopting secure access controls, using modern collaboration tools, and promoting a culture of security awareness, organizations can protect their sensitive documents without sacrificing productivity.
Remember, every password shared is a potential door left wide open. Closing that door starts with understanding the stakes and choosing safer alternatives.
Looking for better ways to manage your business contacts securely? Happierleads provides secure access to over 175 million verified B2B contacts with enterprise-grade security features to keep your data safe.
You might also like
Website Identification FAQs
Does Happierleads have a Free trial?
What is Happierleads?
Happierleads is the only solution that enables you to identify, qualify, and engage with your anonymous B2B website visitors—all within a single tool. No additional licenses or integrations with other outreach automation tools are necessary.
Who typically uses Happierleads?
Happierleads is used by Sales, Growth, and Marketing teams across various industries. If you are a B2B company, we are the solution for you. Sales teams use the platform to turn anonymous traffic into opportunities and increase productivity. Marketers use the platform to automate lead generation and increase conversions.
How is this different from Clearbit, 6Sense, or DemandBase’s Website Identity Solutions?
Most companies rely on ‘Reverse IP Lookup’ technology to connect IP addresses with company names. At Happierleads, we use a completely different approach—our fully-permissioned, proprietary publisher network—allowing us to identify the exact individuals visiting your website. Discover more about how we identify your site visitors here.
Why is Happierleads ranked number #1 for data quality on G2 and Capterra?
Happierleads offers an advanced feature that automatically filters out bots, ISPs, and other non-qualifying traffic sources to ensure you receive only high-quality leads. Additionally, unlike other tools, Happierleads provides the flexibility for you to manually remove leads as needed.
What about U.S. state privacy laws, like the California CCPA and CPRA?
How accurate is the visitor identification?
Most reverse-IP tools only identify the company. We go further — using our permissioned publisher network we identify the exact person behind the visit and enrich them with verified work email and LinkedIn data. Match rates depend on traffic geography, but customers typically see person-level identification on 30–55% of B2B sessions and company-level on 80%+.
How long does setup take?
About 5 minutes. Sign up, paste a single tracking snippet into your site (or install our GTM template / WordPress plugin), and identified visitors start appearing in your dashboard within a few hours. No engineering project required.
What if my website doesn't get much traffic?
You don't need huge traffic to win — most of our customers have under 10,000 monthly visitors. Even on lower-traffic B2B sites a handful of identified buyers per week often pays for the tool many times over. You can also pair it with our 175M-contact database and outreach engine to build pipeline beyond just your site visitors. And if your own traffic is still growing, we also provide third-party intent signals — data from across the web that tells you which companies are actively researching solutions like yours right now, so you can reach them even before they land on your site.
Does it integrate with my CRM and outreach tools?
Yes. Push identified leads directly into HubSpot, Salesforce, Pipedrive, Zoho, GoHighLevel, Slack, or anything that supports Zapier and webhooks. CSV export is available on every plan, and our built-in email and LinkedIn outreach engine lets you act on identified visitors without leaving Happierleads.




